Are you ready to use your phone as your electronic wallet? Have you heard the idea of paying for goods & services just by tapping your smartphones at the payment counter? If you are unaware of the concept of mobile payments, you need to know that this is the new payment system that uses your NFC enabled smartphone devices and turns them into wallets.
For novices, mobile wallets allow you to make payments through your mobile phones, easily, conveniently and most securely.
Mobile Payment technology masks your bank details in 3 additional layers before your financial details reach your smart phone. Your first step for operating the mobile transaction is to setup your payment wallet online. This wallet contains the financial data or your credit card information that you store online and is accessible only through your PIN code and Password that you generate.
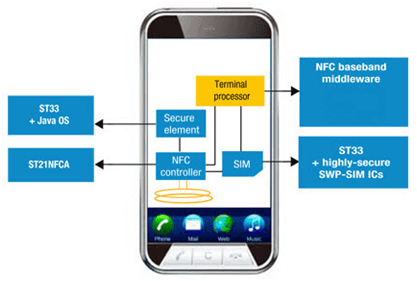
Once your online wallet is setup, the next step is to setup your TSM. The Trusted Service Manager (TSM) is a role that acts as a neutral broker and enables the communication between your mobile network operators, phone manufacturers or other entities controlling the secure element on mobile phones. However, remember, this is a background process that facilitates your mobile payment capability. The core function of TSM is to manage the process of acquiring your financial data and authorizing it for secure payment processing. This core component hence also monitors your financial accounts during the process of payments; and validates your acceptability for the retailer during transaction. So, once the TSM syncs through your mobile wallet and on to your NFC Chip on your phone, you are good to go. Remember, cellular networks are hard to crack. These are complex networks with real-time encryption facility that operate securely and effectively. Hence, for a hacker, to break through your mobile network is next to impossible, if I may be so bold to say.
Once your wallet is synced with your TSM and your TSM coordinates with your Mobile Network, the fourth component that is used is your NFC Chip, through which your payments are provisioned. Remember, all data is transferred through encryption so the merchants cannot steal your data. Second, your NFC validates your identity through a Pin Code protection so only you have the key or password to your money. Moreover, the chip in your phone prevents accidental or intentional tampering and will deny unauthorized access.
The key here is that the NFC does not have access to any data on your phone. A hacker could hack your NFC chip password. But that is as far as the hacker could go. They would not be able to make any transactions as background security system must authorize transactions before they can be made.
This is an easy to use technology that is powerful and integrates your entire bank details in your phone. All the service providers are easy to understand, install and manage.